Police in Italy and France have made a number of arrests in reference to an over $14 million assault on crypto protocol Holograph.
In an in depth publish on X on Aug. 14, the omnichain tokenization platform said that legislation enforcement authorities in France and Italy had made a number of arrests of people suspected to have been behind the theft of 1 billion of its native tokens, valued at 13 million euros (about $14.4 million).
In accordance with the group behind Holograph (HLG), investigations into the incident have been led by the Workplace for the Prevention of Cybercrime and the Brigade de Répression du Banditisme in France. It additionally bought help from Europol, Italy’s Directorate of Anti-Mafia Investigations, and the Cayman Islands police.
French publication Le Parisien described the suspects as Jap Europeans of their 30s, reporting that they’d been arrested in Italy and have been awaiting extradition to France. It was additionally mentioned that authorities had seized electronics and frozen funds belonging to the suspects.
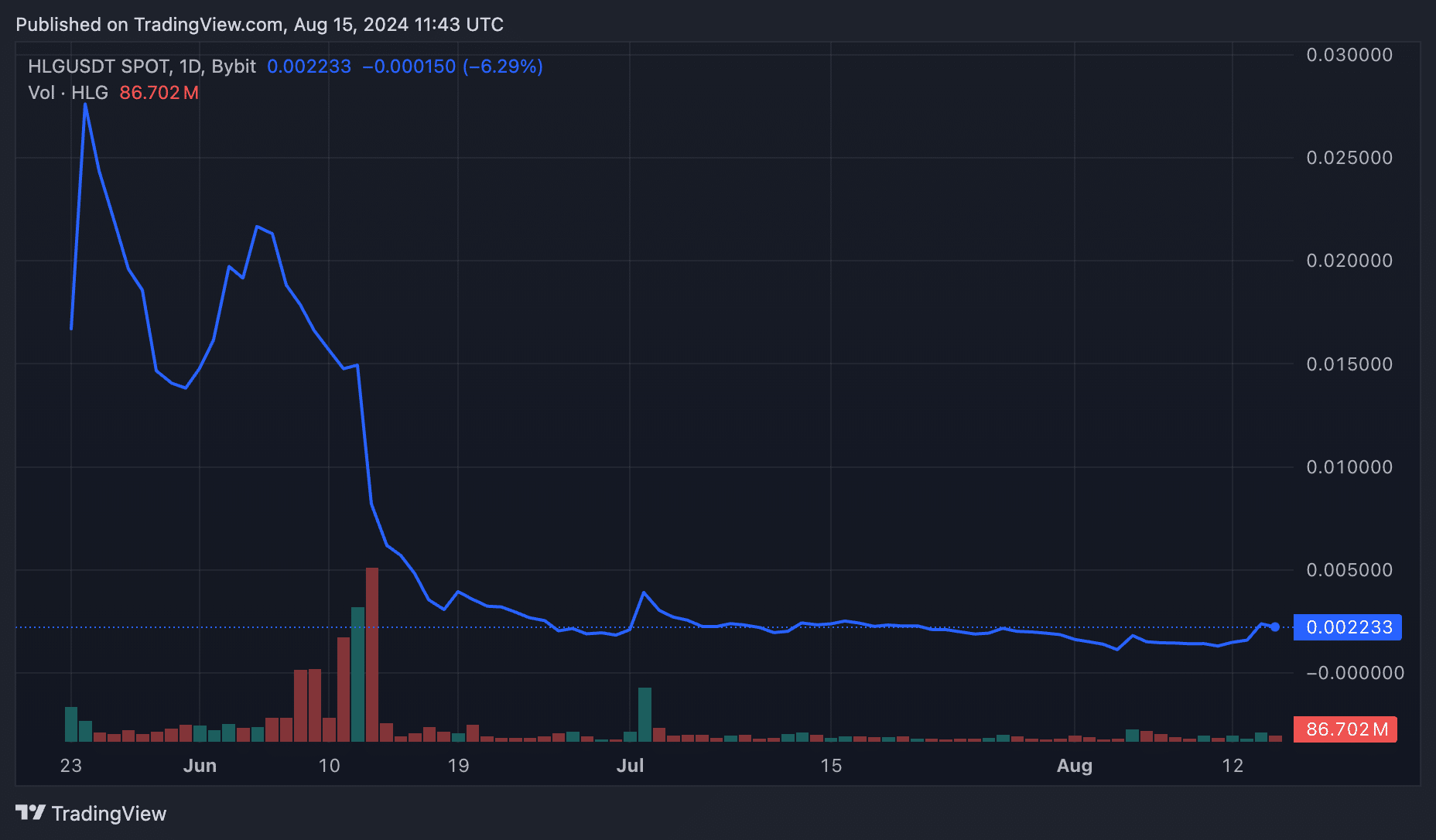
The hack occurred on June 13, with the attackers exploiting Holograph’s operator contract to mint a billion HLG tokens utilizing a proxy pockets.
Following the incident, HLG misplaced greater than 80% of its worth, dropping to a low of $0.0029. Knowledge from crypto.information reveals that the token has principally traded under $0.003 because the assault, solely briefly hitting $0.049 on July 2, a date that coincided with Holograph’s launch of a autopsy report of the assault.
On the time of writing, HLG was priced at $0.00231, a 28% enhance over the previous 24 hours. The token is up nearly 60% on the week.
The autopsy discovered {that a} “disgruntled former contractor” of the platform was accountable for the exploit. The contractor allegedly used their administrator entry to insert malicious jobs into the platform’s sensible contract, which they then executed on June 13.
Moreover, information from Etherscan confirmed that the attacker transformed the stolen funds into Tether (USDT) solely hours after the exploit.
The platform has since then carried out operational threat controls geared toward stopping such incidents from taking place sooner or later.